What Happens to Your IT Equipment After It’s Recycled?
Summary
The journey of recycled IT equipment is a highly regulated and documented lifecycle that transforms retired hardware into either refurbished assets or recovered raw materials. This process begins with a rigorous chain of custody and intake assessment, followed by non-negotiable data destruction methods like degaussing or physical shredding to mitigate breach liability.
Most organizations retire technology assets every few years. Hard drives fill up, servers become outdated, and workstations get replaced. But what actually happens after that retired gear leaves your facility? The journey of recycled IT equipment is more regulated, more documented, and more consequential than most people realize. Understanding the full lifecycle of a retired asset helps organizations make informed decisions about who handles their technology and how.
The First Step: How IT Equipment Is Collected and Sorted
When a certified IT Asset Disposition (ITAD) provider picks up your retired assets, the process begins with intake and categorization. The team logs, tags, and assesses each device for condition and reuse potential. This step establishes a chain of custody, which is the documentation trail that tracks every asset from pickup to final disposition.
Sorting determines what happens next. Assets in functional condition may qualify for refurbishment and resale. Devices too degraded for reuse move toward material recovery. This initial triage is critical. It sets the course for every subsequent decision in the disposition process.
Data Destruction Before Recycling Begins
No piece of equipment moves forward in the recycling workflow until the team confirms data destruction. This is a non-negotiable step, regardless of whether a device appears wiped or inactive.
Certified ITAD vendors use multiple methods depending on the device type:
Degaussing. Exposing magnetic media to a powerful electromagnetic field to render data unreadable
Physical shredding. Mechanically destroying drives and SSDs beyond any possibility of recovery
Software overwriting. Applying DOD-compliant or NIST 800-88-aligned wipe protocols for devices designated for reuse
Each method generates a verified proof of destruction. This record supports regulatory compliance with frameworks such as HIPAA, SOX, and GDPR. Without confirmed destruction certificates, companies remain exposed to data breach liability even after hardware leaves their premises.
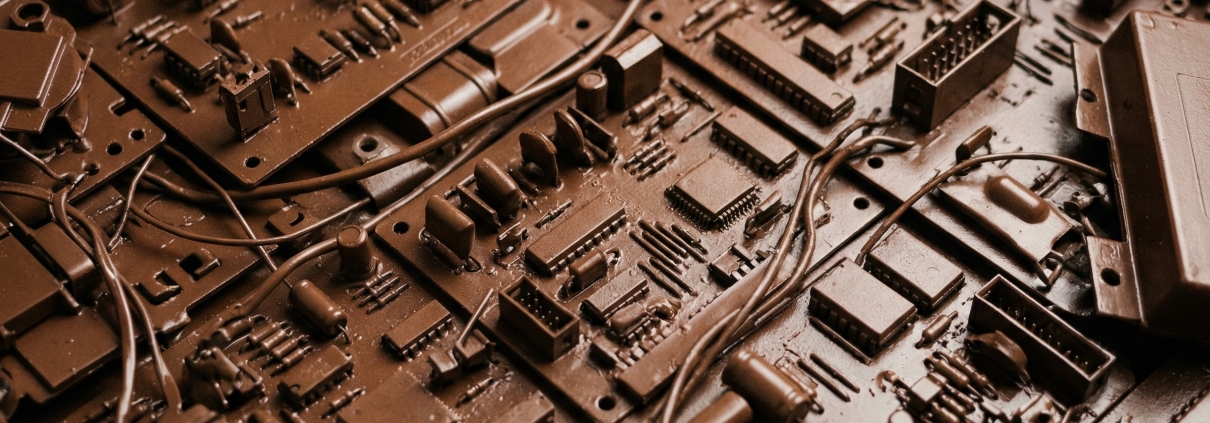
Breaking Down IT Equipment: What Happens to the Materials
Once data is securely destroyed, devices enter the material recovery phase. Modern electronics contain a range of recoverable resources. Recyclers extract copper, aluminum, gold, silver, and rare earth elements and reintroduce them into manufacturing supply chains.
The breakdown process follows a deliberate sequence. Technicians remove hazardous components first, including batteries, capacitors, and mercury-containing displays. These require separate handling under EPA and state-level environmental regulations. The team then shreds or disassembles remaining components for sorting by material type.
Recovered metals and plastics are sold to smelters and processors. This offsets disposition costs and, in some cases, generates revenue returned to the originating company. Recovery potential depends on asset volume and condition, current commodity markets, and the capabilities of the ITAD provider.

What cannot be recycled must be disposed of in compliance with local, state, and federal environmental standards. Responsible providers maintain clear records of all material flows throughout the process.
Certifications and Compliance in the Recycling Process
Not all recyclers operate at the same standard. Certifications exist to differentiate providers that follow rigorous environmental and data security protocols from those that do not.
R2 (Responsible Recycling) certification is one of the most recognized credentials in the industry. It governs how providers handle data destruction, vendor oversight, environmental health and safety, and worker protections. ISO 14001 certification signals a formal environmental management system. NAID AAA certification validates data destruction practices specifically.
These credentials matter because they are independently audited. A certified provider cannot simply claim compliance. They must demonstrate it through regular third-party reviews and thorough recordkeeping. For companies subject to regulatory oversight, working with credentialed partners is not optional. It is a risk management imperative.
Make Every Retired Asset Work for Your Organization
RAKI Computers operates as an R2-certified ITAD provider with nationwide logistics capabilities. Every asset processed through our program follows a documented chain of custody from pickup through final disposition. Data destruction is verified and certificate-backed. Material recovery is transparent, with tracking available for audit purposes.
Organizations that partner with RAKI gain more than a pickup service. They gain a managed, audit-ready program that reduces environmental liability, supports regulatory alignment, and recovers value from retired technology. The lifecycle of your IT equipment does not have to be a burden. With the right partner, it becomes a controlled, compliant, and financially strategic process.
Reach out to RAKI Computers to learn how our ITAD solutions can support your technology lifecycle management.



Leave a Reply
Want to join the discussion?Feel free to contribute!