The Hidden Risk Mitigation Benefits of Professional ITAD Services
Summary
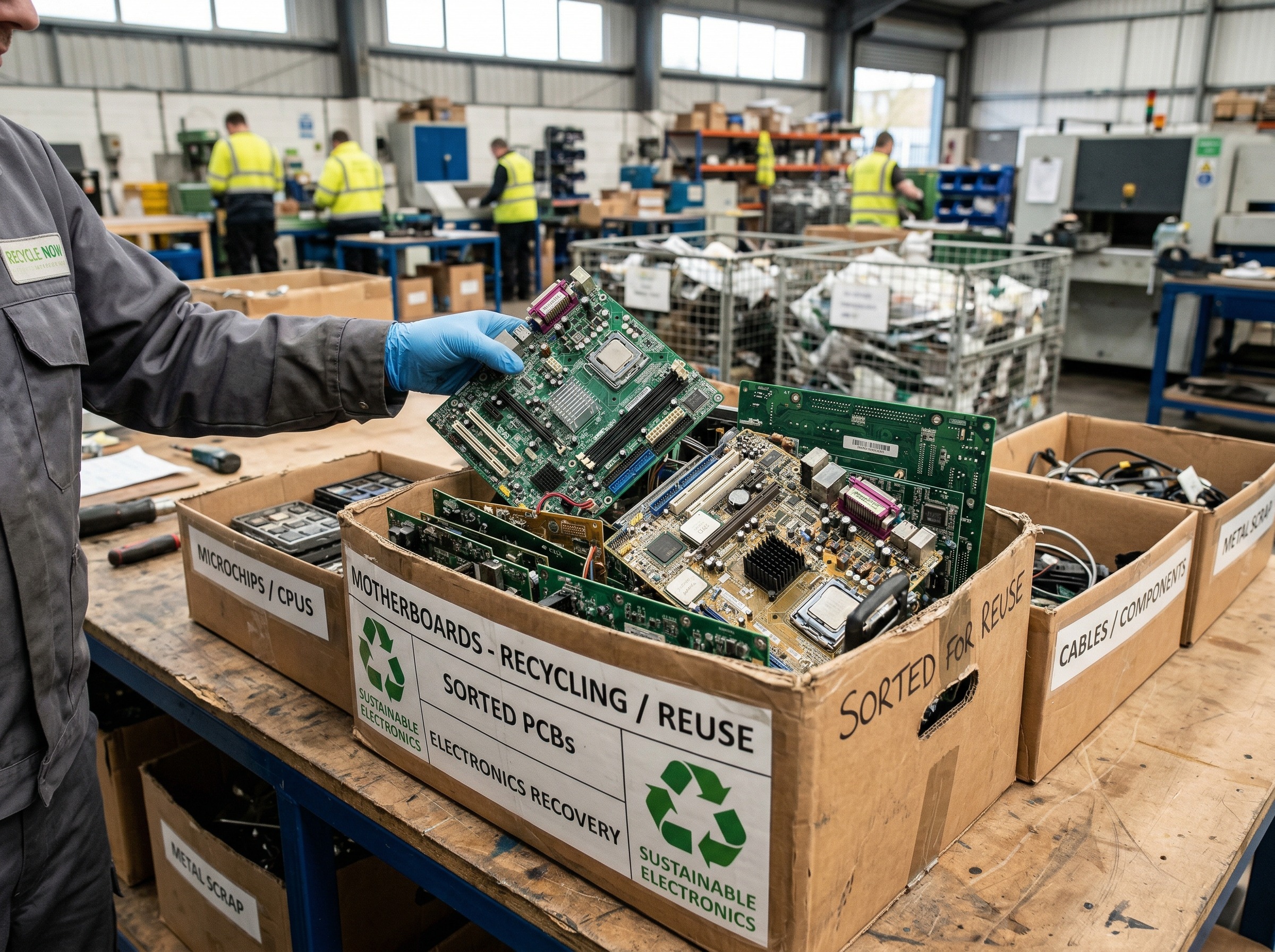
ITAD services, or IT Asset Disposition, represent a strategic risk management function designed to address the significant vulnerabilities associated with retiring technology. While many companies treat old hardware as a simple logistical inconvenience, professional ITAD protocols mitigate critical risks—including data breaches from improperly destroyed media, regulatory penalties from undocumented workflows, and environmental liabilities. By utilizing certified destruction methods and providing audit-ready documentation, these services transform a routine disposal task into a defensible governance process.
Most companies treat retired technology as a logistical inconvenience. Old laptops pile up. Servers get pushed to storage rooms. Hard drives sit in boxes, waiting for someone to act. This approach carries serious, often underestimated risks. ITAD services, or IT Asset Disposition, exist precisely to address these vulnerabilities. Yet many decision-makers still view ITAD as a disposal exercise rather than a strategic risk management function.
Why Risk Mitigation Is Central to ITAD Services
Retiring IT assets is not simply a matter of clearing out old hardware. Every decommissioned device is a potential liability. Data may still reside on storage media. Chain-of-custody gaps can expose businesses to regulatory scrutiny. Improper disposal can also trigger environmental violations.
Risk mitigation is not a secondary benefit of professional ITAD services. It is the core function. A well-structured ITAD program addresses multiple categories of risk at once. These include:
Data security risk from unwiped or improperly destroyed storage media
Regulatory and compliance risk from undocumented disposal workflows
Environmental liability from improper electronics recycling
Reputational harm from data breaches tied to retired assets
Each category carries real financial and material consequences. A single breach originating from a decommissioned device can cost millions in remediation, fines, and lost client trust.
The Data Security Threats Hidden in Decommissioned Equipment
Decommissioned hardware holds more sensitive data than most enterprises realize. Simply deleting files or reformatting a drive does not permanently erase information. Sophisticated recovery tools can reconstruct data from drives that appear wiped.
This is a well-documented vulnerability. Research across multiple years shows that a significant share of second-hand drives sold on the open market still contain recoverable data. The problem extends beyond laptops and desktops. Copiers, printers, and networking equipment also retain sensitive information.
Professional ITAD protocols employ certified data destruction methods. These include overwriting procedures, degaussing, and physical shredding. Each method is matched to the classification level of the data involved. Records are generated at every stage, creating a defensible audit trail.
Firms that lack this discipline are exposed. Data destruction cannot be done halfway.
Regulatory Exposure and the Compliance Gap
Data privacy regulations have expanded considerably. HIPAA, GLBA, FACTA, state-level privacy laws, and frameworks like GDPR all carry provisions tied to data disposal. Non-compliance is not just a legal concern. It also signals governance immaturity to auditors, partners, and clients.
Many decision-makers assume internal IT teams can handle asset retirement adequately. However, internal efforts rarely produce the comprehensive reporting that regulators require. Audit-ready reports, certificates of data destruction, and chain-of-custody documentation are standard deliverables of professional ITAD initiatives. Internal teams seldom match this standard.
The compliance gap is often invisible until an audit or incident forces it into view. At that point, the absence of proper records becomes a significant liability.
How Professional ITAD Services Strengthen Organizational Resilience
Risk management is not just about preventing breaches. It is about building resilience into how an enterprise operates. A company that retires assets with rigor demonstrates mature governance. This matters to clients, partners, and regulatory bodies alike.
Professional ITAD services contribute to resilience in several important ways. They reduce the attack surface associated with retired hardware. ITAD services also ensure sensitive data does not re-enter circulation through secondary markets. They also equip businesses with the records needed to respond quickly and credibly during audits or incidents.
Resilience extends to logistics as well. Managing large volumes of retired equipment across multiple sites is complex. Coordinated, secure removal and transport minimize the exposure window throughout the decommissioning phase.
This is where RAKI Computers delivers measurable value. As an R2-certified ITAD provider, RAKI combines certified data destruction, nationwide logistics, and structured reporting into a cohesive solution. The result is a disposition process that actively reduces risk rather than simply clearing out obsolete hardware.
Make Risk Management Part of Your IT Lifecycle Strategy
Retiring technology assets carries more risk than most companies plan for. Unaddressed, these vulnerabilities compound with every decommissioning cycle. A professional ITAD program transforms a routine task into a strategic risk management function.
RAKI Computers helps businesses across all industries build that capability. From single-site operations to multi-location enterprises, RAKI’s nationwide ITAD services deliver the security, compliance documentation, and audit-ready reporting your firm needs. These capabilities protect your enterprise at every stage of the asset lifecycle. Reach out to RAKI today to learn how we can support your IT risk management strategy.




Leave a Reply
Want to join the discussion?Feel free to contribute!