5 Critical Steps for Secure Data Center Equipment Decommissioning
Retiring a data center is rarely as straightforward as pulling plugs and hauling hardware. Whether a company is migrating to the cloud or consolidating facilities, equipment decommissioning demands deliberate planning. A single misstep can expose sensitive data, trigger regulatory penalties, or create significant environmental liability. The stakes are particularly high when companies involve data-bearing equipment. This guide outlines five critical steps that IT and operations leaders should follow to execute a secure, compliant, and efficient decommissioning project.
#1: Conduct a Thorough Asset Inventory before Equipment Decommissioning
The foundation of any successful equipment decommissioning project is a complete, verified asset inventory. Every server, storage array, switch, and peripheral must be cataloged before a single device leaves the facility. This includes devices that are easily missed during a complex, large-scale transition.
An accurate inventory serves multiple functions. It establishes a documented chain of custody, supports audit readiness, and ensures that no assets are overlooked during disposition. Teams should record serial numbers, asset tags, data-bearing status, and physical location for each item. Skipping this stage often results in documentation gaps that develop into serious compliance problems during a future audit.
#2: Develop a Certified Data Destruction Strategy
Not all devices store data in the same way, and not all destruction methods are equally effective. A structured sanitization strategy must account for media type. This includes hard disk drives, solid-state drives, magnetic tape, and embedded storage within networking equipment.
Accepted approaches include:
Certified degaussing for magnetic media
NIST 800-88-compliant overwriting for drives intended for reuse
Physical shredding or crushing for devices that cannot be sanitized electronically
Each method must produce verifiable certificates of destruction. These certificates are essential for regulatory compliance and internal governance reviews. Without them, an enterprise cannot demonstrate that sensitive information was handled according to accepted protocols.
#3: Align Decommissioning Activities with Compliance Frameworks
Data privacy regulations and industry-specific standards impose strict requirements on how businesses handle data-bearing assets at end of life. HIPAA, GLBA, SOX, and state-level privacy statutes all carry specific obligations tied to secure asset retirement. Failing to account for applicable frameworks early in the preparation process can create significant downstream consequences.
Compliance alignment during equipment decommissioning is not optional. Enterprises that neglect proper protocols face monetary penalties, reputational harm, and legal exposure. Audit-ready records should be maintained throughout each phase. These records capture asset inventories, destruction certificates, chain of custody transfers, and final disposition results. A well-structured paper trail demonstrates due diligence and mitigates audit exposure during regulatory reviews.
#4: Plan Secure Logistics for Equipment Decommissioning
Transporting decommissioned hardware from a data center is one of the highest-risk stages of the entire operation. Equipment must be moved carefully to prevent unauthorized access, physical damage, or breaks in chain of custody. A custody gap, no matter how brief, can void compliance documentation and create liability.
Effective logistics coordination must address several key measures. These include tamper-evident packaging, GPS-tracked vehicles, and documented security protocols at each handoff point. Multi-location projects introduce additional complexity. Businesses operating across several facilities need a logistics provider with consistent operational standards. The firm must demonstrate verified capability at every site, not just centrally.
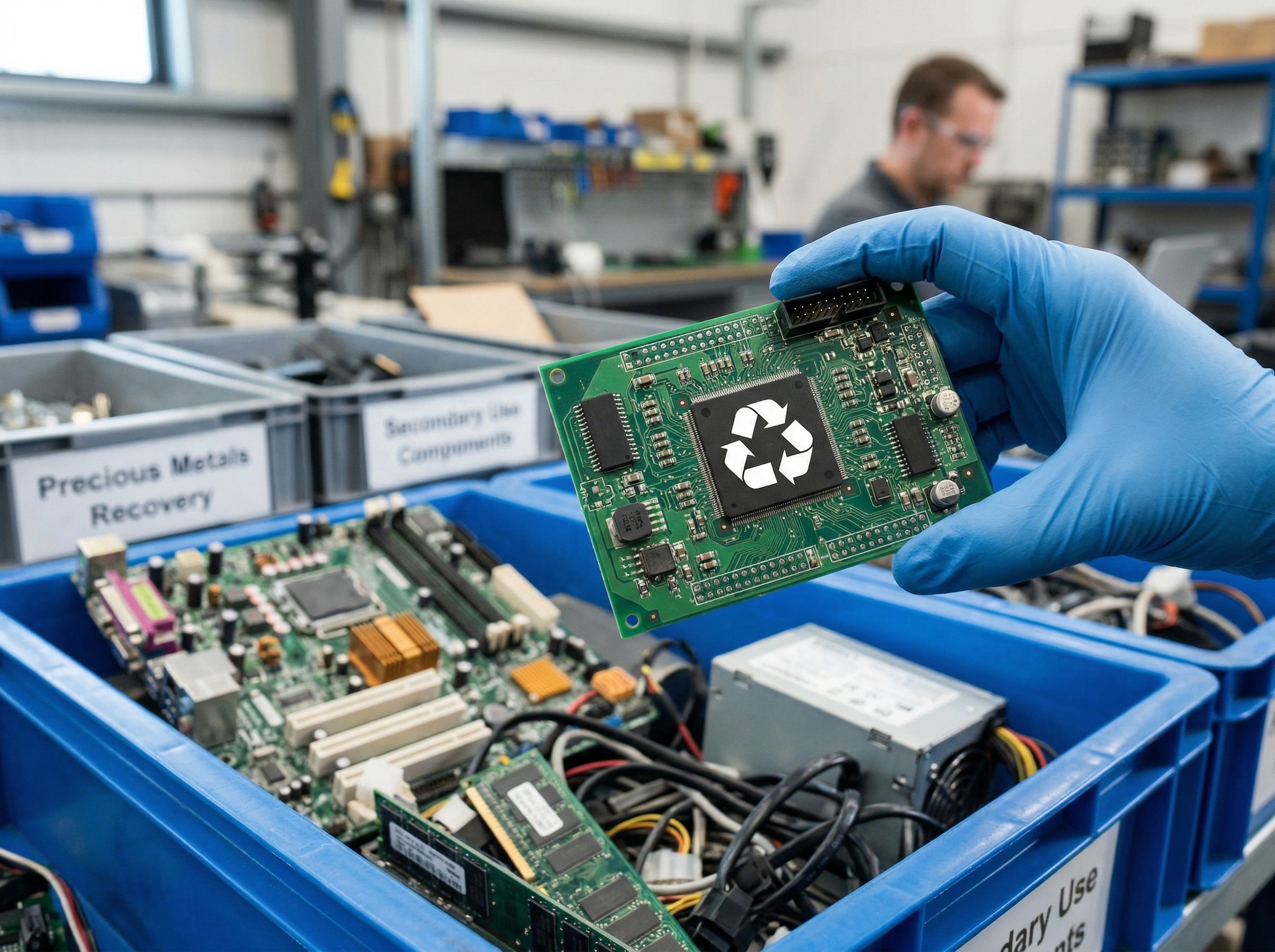
#5: Recover Residual Value and Minimize Environmental Liability
Decommissioned hardware frequently retains market value. A strategic disposition approach can offset project costs through certified remarketing of functional equipment. This transforms what appears to be a sunk cost into a source of measurable return.
Assets with no resale potential still require responsible handling. Improper disposal creates environmental liability under EPA regulations and international e-waste criteria. Certified recycling programs ensure hazardous materials are processed correctly. Clear reporting on recovered value, recycling fees, and disposal costs gives leadership a complete picture of the project’s financial outcome. For organizations with ESG commitments, this documentation also supports sustainability reporting.
Take the Next Step with a Certified ITAD Partner
Executing these five steps demands deep expertise, specialized resources, and verifiable credentials. An experienced IT Asset Disposition partner brings the infrastructure and accountability that internal teams often lack when managing large-scale decommissioning.
RAKI Computers is an R2-certified ITAD provider delivering secure, compliant, and environmentally responsible technology lifecycle solutions nationwide. RAKI supports enterprises through every stage of data center equipment decommissioning. Services span certified data destruction, audit-ready reporting, coast-to-coast logistics, and strategic value recovery.
For IT leaders with a pending project, engaging a qualified ITAD vendor early reduces risk. It also improves compliance posture and drives better financial results. Contact RAKI Computers to learn how your organization can approach decommissioning with confidence.




Leave a Reply
Want to join the discussion?Feel free to contribute!