Protecting Sensitive Data on Retired Networking Gear and Switches
Summary
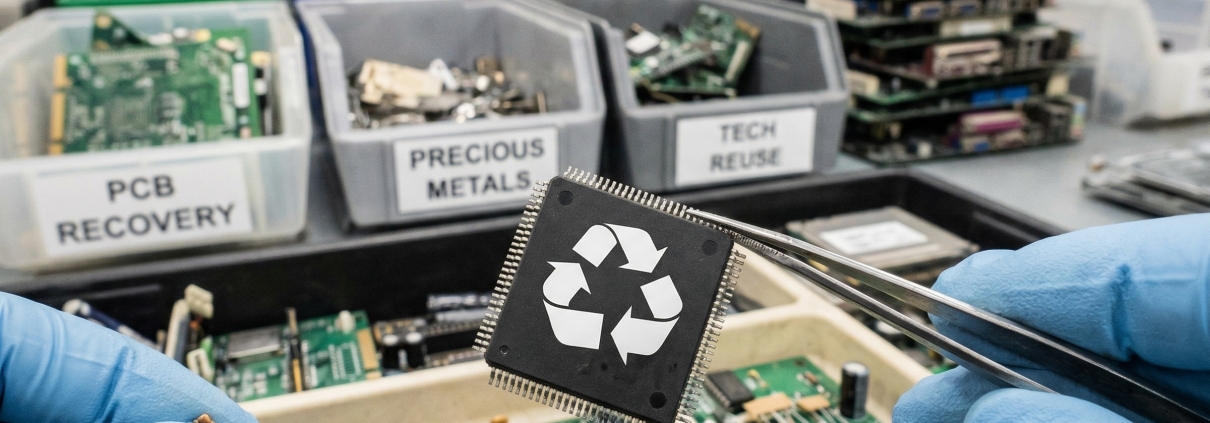
Protecting sensitive data on retired networking gear—such as routers, switches, and firewalls—is frequently overlooked by IT teams who prioritize servers and workstations . Unlike basic consumer devices, enterprise networking hardware retains persistent configuration files, SNMP community strings, and privileged access credentials in flash memory and NVRAM that survive standard factory resets . Without a certified decommissioning strategy involving cryptographic erasure or physical destruction, these assets can reveal internal IP schemes and security policies to unauthorized parties.
When most IT teams plan for data sanitization, the focus falls on servers and workstations. Networking equipment, however, tends to fly under the radar. Routers, switches, firewalls, and load balancers store more sensitive information than many professionals realize. Overlooking these assets during decommissioning creates serious compliance and security exposure. Protecting sensitive data across all retired technology requires a deliberate approach that includes networking infrastructure, not just endpoint devices. Leaving networking gear out of the equation is a gap that threat actors and auditors alike are quick to identify.
Why Networking Devices Carry Hidden Data Risks
Enterprise networking equipment is more than a traffic conduit. These devices retain configuration files, credentials, and topology details that persist long beyond their active service life.
Routers store access control lists, SNMP community strings, and authentication credentials. Managed switches log MAC address tables and VLAN assignments. Firewalls hold policy rules, VPN configurations, and user access records. Even after a standard factory reset, forensic tools can retrieve residual data from flash memory and NVRAM. The reset operation may remove pointers to stored information without permanently eliminating it.
The risk is well-documented. Researchers have demonstrated that used enterprise networking gear purchased on the open market frequently contains recoverable configuration data. A single decommissioned switch can reveal internal IP schemes, segmentation policies, and privileged access credentials. That level of exposure is a significant breach vector that many organizations fail to account for.
Protecting Sensitive Data Starts Before Decommissioning
A secure disposition workflow should begin well before a device leaves the rack. Waiting until hardware reaches a staging area is too late. Teams that delay sanitization planning until the final step introduce avoidable risk.
A proactive framework includes:
Conducting a full asset inventory to locate every networking device, including those at remote or branch sites
Documenting firmware versions, stored settings, and associated access information for each asset category
Assigning clear accountability for sanitization procedures before any hardware is relocated or removed
Too often, networking gear is bundled with other outgoing hardware and handed off without a device-specific protocol. Each asset category demands its own sanitization method. A generic, one-size-fits-all approach is insufficient.
The Problem With Factory Resets and Internal Procedures
A persistent misconception is that a factory reset adequately wipes a networking device. For most enterprise-grade hardware, this is simply not true. Flash memory and NVRAM can retain data even after a reset is performed. The operation removes pointers to stored information rather than destroying it.
Internal IT staff managing sanitization manually introduce additional variables. Without standardized workflows, there is no guarantee that each piece of equipment receives consistent treatment. These inconsistencies create audit gaps that surface during regulatory reviews or post-incident investigations.

Compliance frameworks such as HIPAA, NIST SP 800-88, and PCI DSS require verifiable, auditable evidence of data destruction. Internal methods performed without certified oversight rarely satisfy these requirements. The consequences extend beyond regulatory penalties. A data breach traced to improperly decommissioned networking infrastructure can damage client relationships and erode professional trust.
Certified Destruction Standards for Protecting Sensitive Data
Certified data destruction goes considerably further than a reset or manual wipe. Depending on the device type, the method may involve cryptographic erasure, physical media destruction, or both. The choice depends on the sensitivity of the information the hardware processed.
For assets where software-based sanitization is not viable, physical destruction of storage components is the only defensible path to compliance. Each step must be linked to specific asset serial numbers. Certificates of destruction issued for each unit form the foundation of an audit-ready disposition record.
Third-party verification adds credibility that internal procedures cannot replicate. An independent, certified provider validates that destruction aligns with applicable regulatory requirements. That documentation becomes essential when demonstrating due diligence to auditors, legal counsel, and executive stakeholders. It also shields the organization against post-disposition disputes and investigations.
Take Control of Your Networking Asset Lifecycle
RAKI Computers provides enterprise clients with a structured, R2-certified approach to IT asset disposition across all industries. Comprehensive data destruction services cover networking hardware of every type. This includes core switches, edge routers, firewalls, and security appliances.
Every asset processed receives documented sanitization tied to individual serial numbers. Clients receive granular disposition reports that directly support audit readiness and reduce liability when retiring infrastructure at scale.
Networking asset decommissioning does not have to introduce security risk. With a qualified, certified ITAD partner, it becomes a controlled, compliant, and financially recoverable process. Connect with RAKI Computers to learn how your team can decommission networking assets while maintaining full security and regulatory compliance.



Leave a Reply
Want to join the discussion?Feel free to contribute!